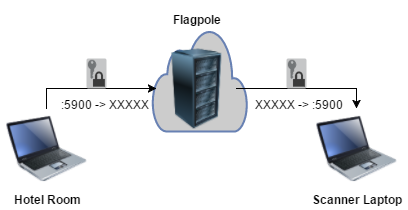
There are three computers in this setup, which takes about 5 minutes.
- The laptop on the client network (the VNC server)
- The laptop you want to connect to the remote desktop with (the VNC client)
- A flagpole server (Internet-facing SSH server)
Localhost port forwards managed by the Flagpole server sets up a secure tunnel between the machines.
No new ports will be externally exposed on any of the machines, and all network traffic will be encrypted through SSH. This method is preferable to other remote desktop solutions such as TeamViewer, where essentially the Flagpole server is controlled by a third party. For extra security, you can run your Flagpole SSH daemon on a high port and enforce certificate-based authentication.
This guide is for Linux, but the general methodology is probably possible on Windows using TigerVNC and PuTTY.
Step 1: Bind VNC Server to the Flagpole
On the VNC server machine (scanner laptop), issue the following commands:
tmux new
x11vnc -localhost [-forever]
<ctrl+b, c>
ssh -R XXXXX:localhost:5900 user@yourserver.com
Replace XXXXX with an unused port on Flagpole. Note that it is also possible to set a password for the x11vnc server. x11vnc defaults to port 5900, but can be changed with i.e. x11vnc -rfbport ###. This port is now forwarded by the port you assigned on the Flagpole.
Step 2: Bind Flagpole to VNC Client
On the VNC client (from your hotel room)
tmux new
ssh -L 5900:localhost:XXXXX user@yourserver.com
Where XXXXX is the port you bound on Flagpole. This forwards port 5900 on your local machine to the port you assigned on Flagpole.
Step 3: Connect VNC Client to VNC Server
Now, open your VNC software (vinagre/vncviewer/etc.) and connect to localhost:5900
No comments :
Post a Comment